Review Number Mapping 9362460049 Securely
Review Number Mapping 9362460049 represents a critical framework for enhancing consumer feedback integrity. Its secure implementation relies on advanced encryption and stringent access controls. By protecting sensitive information, organizations not only prevent unauthorized access but also promote honest evaluations. This systematic approach raises questions about the best practices and technologies that can further fortify review management systems. Understanding these elements is essential for fostering accountability and empowering users in their data stewardship.
Understanding Review Number 9362460049
Review Number 9362460049 serves as a unique identifier that facilitates the systematic analysis of feedback associated with a specific product or service.
Its review number significance lies in enhancing the transparency of consumer insights while ensuring secure data handling.
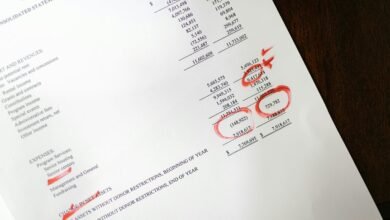
Best Practices for Secure Mapping
Effective mapping of review numbers, such as 9362460049, necessitates adherence to best practices that prioritize security and accuracy.
Implementing robust data encryption safeguards sensitive information during transmission. Additionally, instituting stringent access controls ensures that only authorized personnel can manipulate or view mapping data.
These measures collectively enhance the integrity of the mapping process, fostering an environment conducive to freedom and security in data management.
Tools and Technologies for Data Protection
Data protection relies heavily on a diverse array of tools and technologies designed to safeguard sensitive information against unauthorized access and breaches.
Effective data security incorporates advanced encryption techniques to ensure confidentiality, while adherence to compliance regulations mitigates legal risks.
Organizations must continually evaluate and implement these solutions to foster a secure environment, ultimately empowering users to maintain their freedom in data management.
Implementing a Secure Review Management System
The implementation of a secure review management system necessitates a comprehensive approach that integrates robust security measures from the outset.
Critical components include user authentication protocols and stringent access controls, ensuring that only authorized individuals can access sensitive data.
This structured framework not only enhances data integrity but also empowers users, fostering a secure environment conducive to open and honest feedback while protecting individual privacy rights.
Conclusion
In conclusion, the implementation of Review Number Mapping 9362460049 acts as a vigilant sentinel, standing guard over consumer feedback. By intertwining advanced encryption and stringent access controls, organizations weave a protective tapestry that nurtures trust and transparency. This meticulous framework not only fortifies the sanctity of sensitive data but also cultivates a fertile ground for honest evaluations. As users navigate this secure landscape, accountability flourishes, empowering them to wield their data with confidence and integrity.